University of Sydney Data Breach (December 2025)
University of Sydney Data Breach (December 2025): Hackers stole the personal data of over 13,000 individuals, including staff and students, at the University of Sydney.
KoreWealth
3/5/20263 min read
University of Sydney Data Breach (December 2025)
The University of Sydney Data Breach (December 2025) involved unauthorized access to an internal online code library (a repository primarily used for software development and code storage), where historical personal data files were stored. These files, described as legacy extracts used for testing purposes, contained sensitive information from past records.
Timeline and Discovery
The incident was detected in mid-December 2025 (reports indicate "last week" relative to the public announcement on December 18, 2025), when suspicious activity was identified in the system.
The university's IT security team responded immediately by locking down and securing the affected system to prevent further access.
The breach was limited to this single platform and did not impact other university systems, according to official statements.
The university notified relevant authorities, including the New South Wales Privacy Commissioner, the Australian Cyber Security Centre (ACSC), and education regulators.
Announcement and Official Details
On December 18, 2025, the University of Sydney publicly disclosed the breach via an official statement from Vice President of Operations Nicole Gower. The university expressed regret and emphasized transparency, providing a dedicated support page and FAQs for those affected.
Key details from the university's notification:
Hackers accessed and downloaded historical data files.
As of the latest investigations (reported around the announcement), no evidence showed the data had been used, published, or shared on the dark web.
The university launched a full forensic investigation (expected to continue into 2026) with cybersecurity partners.
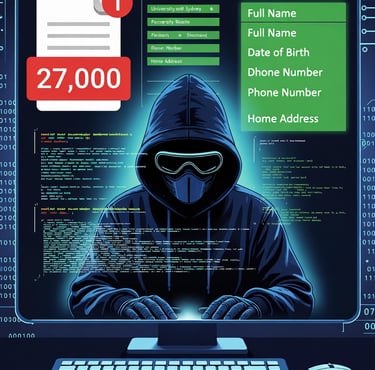
Affected Individuals and Data Exposed
The breach impacted approximately 27,000–27,500 individuals (most sources converged on ~27,000–27,500; early reports sometimes cited lower figures like ~13,000, possibly reflecting initial estimates focused on certain subsets).Breakdown of affected groups:
~10,000 current staff and affiliates (employed or affiliated as of September 4, 2018).
~12,500 former staff and affiliates (from the same 2018 snapshot).
~5,000 former students and alumni (from historical datasets primarily 2010–2019).
A small number (six) of university supporters/donors.
Compromised personal information included:
Full names
Dates of birth
Phone numbers
Home addresses
Employment-related details (e.g., job titles, employment dates)
The data was historical and not from active/current primary systems.
Response and Support Measures
Notifications began with current staff in late December 2025.
Former staff notifications started in the week of January 19, 2026.
Former students/alumni notifications began in the week of January 26, 2026 (once contact details were verified).
The university set up a dedicated cyber incident support page with FAQs, advice on protecting personal information (e.g., monitoring for identity theft, updating passwords, watching for phishing), and contact options.
Affected individuals were encouraged to remain vigilant for potential risks like identity fraud or targeted scams.
Broader Context
This incident highlights risks from "forgotten" or legacy data stored in development environments (e.g., test files in code repos). It was not attributed to a sophisticated exploit but rather unauthorized access to an inadequately segregated or protected repository. No group claimed responsibility, and hacker identity remained unknown at the time of reporting.
For the most up-to-date information, refer to the University of Sydney's official pages:
Main notification: https://www.sydney.edu.au/news-opinion/news/2025/12/18/notification-of-cyber-and-data-breach.html
FAQs and support: https://www.sydney.edu.au/news-opinion/news/2025/12/18/cyber-data-breach-faqs.html
This breach serves as a reminder of the importance of data minimization, secure storage practices, and regular audits of non-production environments in large organizations.(Note: Figures and details are based on consistent reporting from the university and cybersecurity outlets as of early 2026; ongoing investigations may refine these.)