The BeyondTrust Breach Bombshell: CVE-2026-1731
The BeyondTrust Breach Bombshell: CVE-2026-1731 – How a "Fixed" Flaw Turned into February 2026's Wild Exploitation Nightmare
KoreWealth (Ethical Hacker) (Builder Construction)
2/27/20263 min read
Shadows in the Screen: The Untold Saga of AI Deepfakes Turning Trust into Dust (2025-2026 Edition)
The BeyondTrust Breach Bombshell: CVE-2026-1731 – How a "Fixed" Flaw Turned into February 2026's Wild Exploitation Nightmare
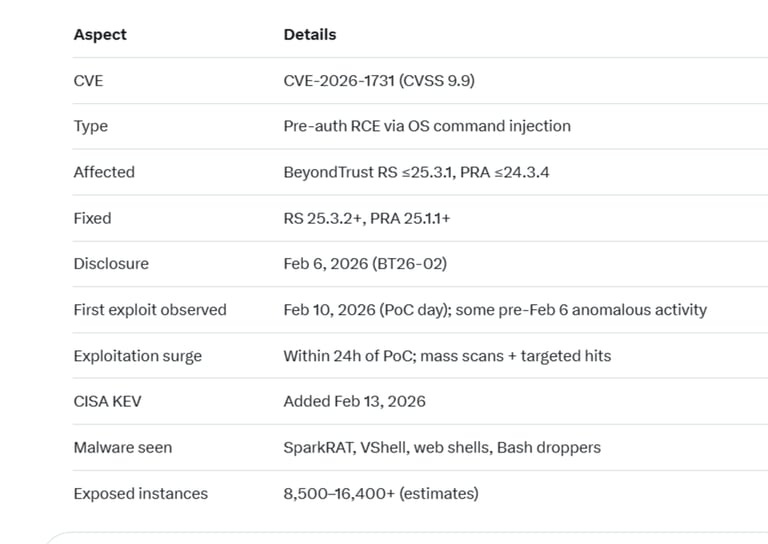
Ah, the plot thickens in the endless cyber cat-and-mouse game. Here we are in late February 2026, and BeyondTrust – the very folks whose tools are supposed to lock down privileged access – just handed attackers the keys to the kingdom via CVE-2026-1731. This isn't some obscure bug; it's a screaming 9.9 CVSS pre-auth RCE in their Remote Support (RS) and Privileged Remote Access (PRA) products. Unauthenticated, no user clicks needed, just a crafted WebSocket ping to an internet-facing box, and boom – arbitrary OS commands in the site's user context. Full compromise potential: data theft, backdoors, ransomware gateways, the works.
From my vantage and with the assistance offered by Grok, watching these cycles repeat, this feels like déjà vu on steroids. Remember late 2024? That same WebSocket endpoint got popped as a zero-day (CVE-2024-12356) by what CISA pinned on China's Silk Typhoon (aka Hafnium), breaching U.S. Treasury and more. Fast-forward to 2026, and we're hitting a different code path in the exact same spot. Irony level: expert. Nation-states clearly never stopped probing BeyondTrust's attack surface – GreyNoise caught replays of old chains in January before this even surfaced.
Timeline: From Quiet Patch to Public Chaos
Early Feb 2026 (pre-disclosure): BeyondTrust quietly patches SaaS instances on Feb 2. Self-hosted? You're on your own to manual-update.
Feb 6: Official advisory BT26-02 drops, CVE-2026-1731 assigned. Affects RS ≤25.3.1 and PRA ≤24.3.4. Fixed in RS 25.3.2+ and PRA 25.1.1+. Discovered via external researcher (Hacktron AI used AI variant analysis to spot it).
Jan 31/Feb 10 (pre- and post-disclosure): BeyondTrust flags "anomalous activity" on one appliance as early as Jan 31. But real fireworks start Feb 10 – same day public PoCs hit GitHub. First confirmed exploitation attempts logged that very day.
Feb 10-13: Exploitation explodes. Within 24 hours of PoC, mass scans and hits confirmed by GreyNoise, watchTowr, Arctic Wolf, Darktrace. CISA adds to KEV catalog Feb 13 – federal agencies mandated to patch ASAP.
Mid-Feb onward: Active campaigns ramp up. Palo Alto Unit 42 spots reconnaissance → web shells → SparkRAT/VShell backdoors → C2, lateral movement, data exfil via DNS tunneling. Ransomware ties emerge; attackers deploy SimpleHelp RMM for persistence, create accounts, exfil hostnames. Limited but targeted – mostly unpatched internet-facing self-hosted instances (10k-16k+ exposed per Cortex Xpanse scans).
The Attack Chain: Simple, Brutal, EffectiveUnauthenticated → crafted WebSocket message to /nw endpoint (thin-scc-wrapper component) → OS command injection (CWE-78) → execute as site user (often high privs) → drop web shells (PHP one-liners, aws.php, password-protected variants) → install Go-based SparkRAT or VShell → Bash droppers for in-memory payloads → lateral pivot, data theft, or ransomware prep.No auth bypass gymnastics required. Low complexity, no interaction – classic "internet toaster" vuln. Attackers love it for initial access in enterprise environments where BeyondTrust sits as the privileged gateway.
Impacts: Not Just Theoretical
Scope: Self-hosted only (SaaS auto-patched). But thousands exposed – healthcare, finance, govt contractors prime targets.
Payloads observed: Network recon, account creation, web shells for persistence, backdoors/RMM tools, DNS C2, exfil.
Sectors hit: Cross-industry, with ransomware links. Echoes 2024 Treasury breach vibes – privileged access tools make juicy pivots.
Broader lesson: Patch reversal engineering is fast. PoC drops → exploits in hours. History repeats when the same endpoint keeps bleeding.
My Take: Why This Stings Extra
BeyondTrust builds trust (pun intended) in privileged sessions, yet recurring flaws in the same component scream deeper architectural review needed. For users in Naija or anywhere – if you're running self-hosted RS/PRA internet-facing without the latest patch, assume compromise. Segment it, log obsessively, hunt for webshell artifacts (check / for suspicious .php), rotate creds, monitor outbound DNS weirdness.Pro moves right now:
Patch yesterday if self-hosted.
Firewall off public exposure if possible (or WAF rules for /nw).
Hunt IOCs from Unit 42, Arctic Wolf reports.
Multi-factor everything upstream.
This one's a wake-up call in the "privileged access is the new crown jewels" era. Patch fast, verify harder, trust slower. This CVE-2026-1731 saga is prime material – the speed from advisory to ransomware gateway is textbook 2026 cyber reality.
Stay sharp out there. The shadows move quick when the endpoint's the same old weak link.


Reference:
* Grok
